In today’s interconnected business world, relying on external vendors and third-party services has become the norm. While this collaboration brings efficiency and specialized expertise, it also introduces a significant layer of security risk to your organization. Every vendor you engage with, from cloud service providers to marketing agencies, becomes an extension of your own attack surface, and a breach originating from their systems can have devastating consequences for your data, reputation, and bottom line.
This is precisely why a robust vendor security assessment process is not just a good idea, but an absolute necessity. Understanding and mitigating these external risks before they materialize is paramount. A structured approach ensures you gather the right information to make informed decisions about who you trust with your sensitive data and critical operations.
Why Your Business Needs a Robust Vendor Security Assessment Process
The digital landscape is fraught with threats, and unfortunately, many significant data breaches don’t originate from within a company’s own four walls, but from vulnerabilities in their supply chain. Think about major incidents you’ve heard about in the news; many of them trace back to a third-party vendor compromise. Without a diligent process to vet your vendors’ security postures, you are essentially leaving a back door open to potential cybercriminals. It’s not enough to simply trust that a vendor has their security in order; you need to verify it.
Beyond the direct threat of a breach, there’s the critical aspect of regulatory compliance. Laws like GDPR, CCPA, HIPAA, and various industry-specific regulations often mandate that organizations ensure their third-party vendors also adhere to specific security standards. Failure to do so can result in hefty fines, legal action, and significant reputational damage. A structured assessment helps demonstrate due diligence to auditors and regulators, protecting your business from legal and financial repercussions.
Furthermore, a proactive vendor security assessment helps you build stronger, more reliable partnerships. When you clearly communicate your security expectations and provide a framework for vendors to demonstrate their capabilities, it fosters transparency and builds trust. It shifts the relationship from a simple service exchange to a collaborative effort focused on shared security and success, ultimately leading to more resilient operations for both parties. It also enables you to identify and address potential weaknesses early on, before they escalate into costly incidents.
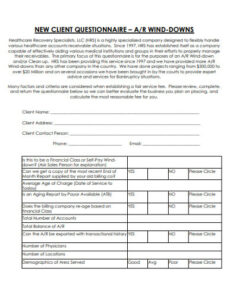
Implementing a consistent process, often facilitated by a comprehensive vendor security assessment questionnaire template, ensures that every vendor undergoes the same level of scrutiny. This standardization removes guesswork, saves time, and provides a clear audit trail of your security review process. It allows your security team to efficiently gather vital information about a vendor’s security controls, practices, and policies, making it easier to compare vendors and prioritize risks.
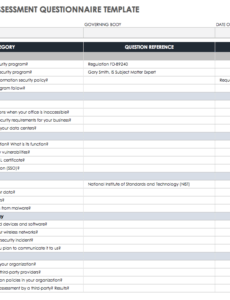
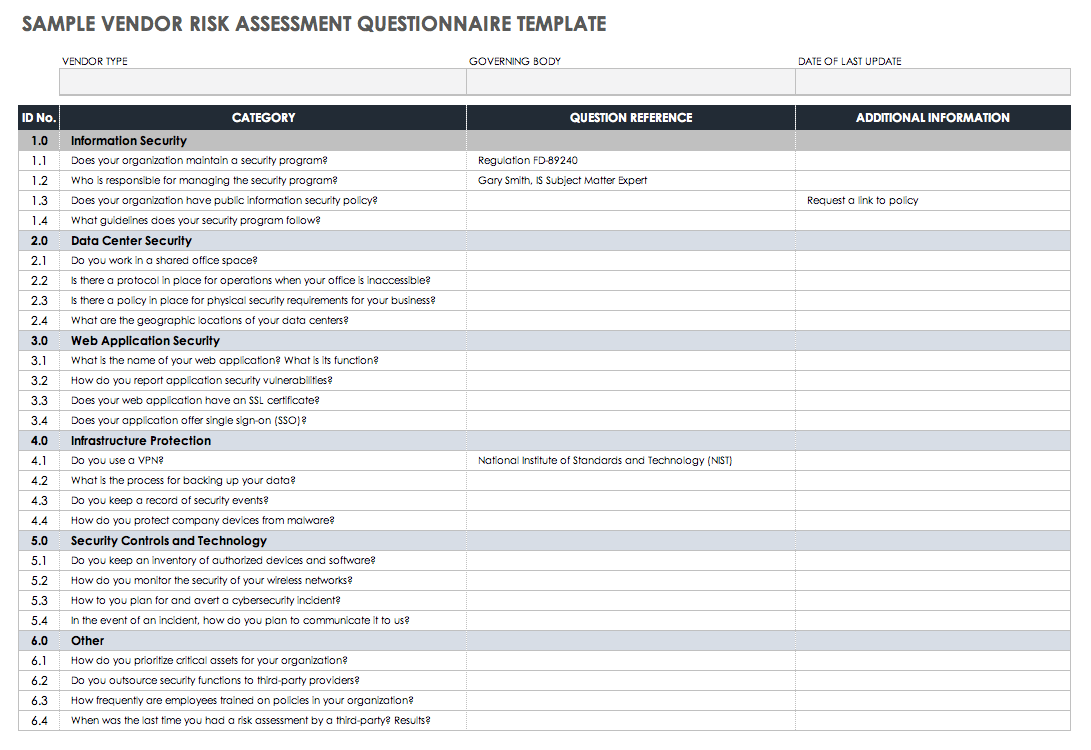
Key Areas a Vendor Security Questionnaire Should Cover
To be truly effective, your questionnaire should be comprehensive yet tailored to the type of vendor and the data they will access or process. Here are some fundamental areas that any good vendor security assessment questionnaire template should explore:
- Data Protection and Privacy: How does the vendor handle, store, and transmit your data? What encryption standards are used? Are there clear data retention and disposal policies?
- Access Control: How does the vendor manage user access to their systems and your data? Are strong authentication methods used? Is there a process for revoking access when an employee leaves?
- Network Security: What firewalls, intrusion detection/prevention systems, and network segmentation strategies are in place? How are network vulnerabilities managed?
- Incident Response and Business Continuity: Does the vendor have a robust plan for detecting, responding to, and recovering from security incidents? How quickly can they restore services after a disruption?
- Compliance and Governance: What industry certifications (e.g., ISO 27001, SOC 2) does the vendor hold? What security policies and procedures are formally documented and followed?
- Personnel Security: How does the vendor screen employees? What security awareness training do their staff receive?
- Physical Security: For vendors with physical infrastructure, what measures are in place to protect their facilities and equipment from unauthorized access?
Building Your Own Effective Vendor Security Assessment Questionnaire Template
While there are many generic templates available, the most effective vendor security assessment questionnaire template will be one that you’ve tailored to your organization’s specific needs, risk appetite, and regulatory landscape. Start by identifying the types of data your vendors will interact with, the criticality of the services they provide, and any industry-specific compliance requirements that apply to your business. This initial scoping will help you prioritize the questions and ensure you’re not asking irrelevant information, or worse, missing crucial ones.
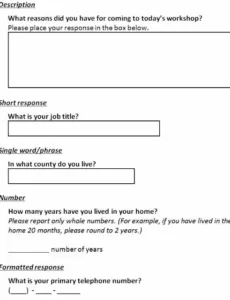
When crafting the questions, aim for clarity and specificity. Avoid vague language that could lead to ambiguous answers. Instead of asking “Is your system secure?” opt for more detailed inquiries like “Describe your patching process for critical vulnerabilities,” or “What multi-factor authentication methods are supported for administrative access?” Providing examples or expected formats for answers can also help vendors provide the information you need efficiently. Remember, the goal is to gather actionable insights, not just check boxes.
A well-designed template is just the beginning; the real value comes from how you use it. Consider establishing a clear process for reviewing the submitted questionnaires, perhaps incorporating a scoring system to objectively evaluate and compare vendors. This allows you to quickly identify higher-risk vendors who might require further due diligence, such as on-site audits or penetration test reports. The information gathered can also serve as a baseline for ongoing monitoring and re-assessment.
Finally, remember that vendor security is not a one-time event. The threat landscape is constantly evolving, and so too should your vendor assessment process. Regularly review and update your vendor security assessment questionnaire template to reflect new threats, changes in technology, and evolving regulatory requirements. Periodically re-assess your critical vendors to ensure their security posture remains strong and aligned with your organizational standards, fostering a continuous cycle of security improvement.
Proactively managing your vendor relationships through a structured assessment process is an investment in your organization’s resilience. It significantly reduces the likelihood of a supply chain attack, protects your valuable data, and helps you maintain compliance with essential regulations. By prioritizing third-party security, you’re not just safeguarding your own assets but also building stronger, more secure partnerships for the future.